Results 41 to 49 of 49
Thread Information
Users Browsing this Thread
There are currently 2 users browsing this thread. (0 members and 2 guests)
-
08-25-2013, 10:12 PM #41Senior Member


- Join Date
- Jan 2006
- Location
- tracking the usurper-in-chief and on his trail
- Posts
- 3,208
Cleaning a disk drive (hiding the evidence)
Windows file deletion renders the file largely inaccessible, but the file itself is not erased and remains on the disk, where snoops and spooks can retrieve it with a variety of disk recovery programs. (You did know that.)
Most freeware disk cleanup programs have a module which fills released or no longer used disk space with blanks or zeroes. Wiping free space to DoD specifications is usually available at a nominal extra cost.
Wise Care 365 (freeware system utilities) includes "Disk Eraser" (on the "Privacy Protector" menu), at no cost. "Disk Eraser" can wipe free space in a user-specified partition or folder using:
- Random Data (1 Pass);
- DoD 5220-22-M (3 passes);
- Schneier's (7 passes); or
- Guttmann (35 passes).
The DoD wipe takes less time than defragmenting the disk, for roughly the same price ($0.00).Last edited by MinutemanCDC_SC; 08-25-2013 at 10:17 PM.
One man's terrorist is another man's undocumented worker.
Unless we enforce laws against illegal aliens today,
tomorrow WE may wake up as illegals.
The last word: illegal aliens are ILLEGAL!
-
08-27-2013, 11:05 AM #42
Grow Your Career With In-Demand Programs From the Leaders in Cybersecurity - 100% Online! Position yourself for success within the booming cybersecurity industry, a field the Bureau of Labor Statistics projects to grow 22% through 2018! Florida Tech's Harris Institute for Assured Information - created through a partnership with the Harris Corporation, a global security leader - is now offering the following career-building credentials 100% online:
- Master of Science in Information Assurance and Cybersecurity
- For-Credit Graduate Certificate in Information Assurance and Cybersecurity
Through the convenience of highly interactive video-based online learning, industry experts will provide advanced knowledge designed to help professionals with technical backgrounds become highly qualified experts in information assurance and cybersecurity.
Info @ http://www.floridatechonline.com/lp/...e5a&mcid=25728Last edited by JohnDoe2; 08-27-2013 at 11:25 AM.
NO AMNESTY
Don't reward the criminal actions of millions of illegal aliens by giving them citizenship.
Sign in and post comments here.
Please support our fight against illegal immigration by joining ALIPAC's email alerts here https://eepurl.com/cktGTn
-
08-27-2013, 03:25 PM #43
Download me IIRemoving the remnants of the Webs most dangerous search terms
Who knew that "free" could lead to a PUP? (Sadly, not the cute and cuddly kind.)
by Conor Myhrvold Aug 25, 2013 10:00 pm UTC
144
 Aurich Lawson
Aurich Lawson
According to McAfees 2008 The Webs Most Dangerous Search Terms, free fell into the highest search term risk category. And my previous search for free stuff on the Internet ended ugly. What did I do? I searched for free things, clicked the top links, and initiated the first download on each page. Thisno surpriseled me to download a bunch of adware and malware, what McAfee coined as Potentially Unwanted Programs (PUPs). For instance, a search for "free music downloads" (the worst search query from round one) left my desktop littered with them. From my download notes and desktop count, I went from three to 19 programs while adding six Firefox plugins and 12 extensions that made my browser a cluttered array of toolbars and icons. My computer was dogged with PUPspoint proven. Now this was my mess to clean up. Could I do anything to fix my computer, and was it even worth it?
Installations from downloading "free music" results:Six Firefox plugins: Conduit Plugin 7.0.0.3, Exent AOD Gecko Plugin 7.0.0.3, GameTreatWidget 8.1.57.0, Google Update 1.3.21.145, Microsoft Windows Media Player Firefox Plugin 1.0.0.8, Shockwave Flash 11.7.700.202I went searching for answers on the Internet and found hints but no conclusions. McAfees white paper Potentially Unwanted Programs: Spyware and Adware, which dates back to 2005 when PUPs were on the rise, hinted at the worst. Anecdotal evidence suggests that many home users and even system administrators periodically wipe out machines and reinstall from scratch or even buy completely new computers to rid them of spyware, adware, and other PUPs. But picking up where I left off, I decided to see for myself just how easy it was to restore my computer to its normal, pristine state if it was possible at all.
12 Firefox extensions: Default Tab 2.0, Frostwire Toolbar 12.42738, MixiDJ V30 10.16.300.3, Mp3skull Toolbar initial.rev194, New Tab 5.0.0.7281, QuickShare Widget 1.1, SavetheChildren App By We-Care.com 4.1.20.1, SearchDonkey 2.6.14, Search-Results Toolbar 1.2.0.0, SelectionLinks 1.5, Yahoo Toolbar 2.5.7.20130322105505, Yontoo 1.20.02
16 programs downloaded: BearShare, Torch (Internet Browser), 24x7 Help, Free Ride Games / 7 Wonders II, FrostWire 5.5.6, Google Drive, Groove-Stream, Adobe Flash, iTunes (didn't install; it was a 32-bit version on 64-bit Windows), iMesh, inTuneMP3, PC Fix Speed, PC Optimizer Pro, SpeedItup Free, The Weather Channel App, WeatherBug
Part I: Just how bad is it?
I resumed my Windows 7 virtualization via Parallels from a more than two-month slumber on my MacBook Pro. Exactly how long had it been? PC Optimizer Pro popped up as soon as I restarted my computer. Last Scan Performed 79 days ago. May 15, 2013 10:37pm. According to this, I had a lot of work to do: 1,286 items. This broke down into 70 Invalid Registry Entries," 629 Junk Files, and 587 pieces of Internet Junk. But since PC Optimizer Pro is adware itself, I didnt trust it. Earlier, it detected problems after a fresh install with almost no other programs, classifying it as scareware.
Still, I did need to update my computer so Id be using a current Windows version. The first 90 updates took more than two hours to download and install. From the Task Manager, adware was the obvious culprit. I was competing with a plethora of processes which I would document to benchmark my adware-infested computer against the results of my soon," but increasingly delayed, un-installation efforts. In the interim, I slogged through adware windows, the first of which was the PC Optimizer Pro notification. It quickly got buried behind other equally urgent offers. SpeedItUp invoked a twist of the childhood fallen food rule, the five-second rule. It would update if you clicked "yes" or after five seconds without you clicking on "no." Given the other program windows that greeted me (weather updates, more fictitious fixes), the Speed It Up install was guaranteed.
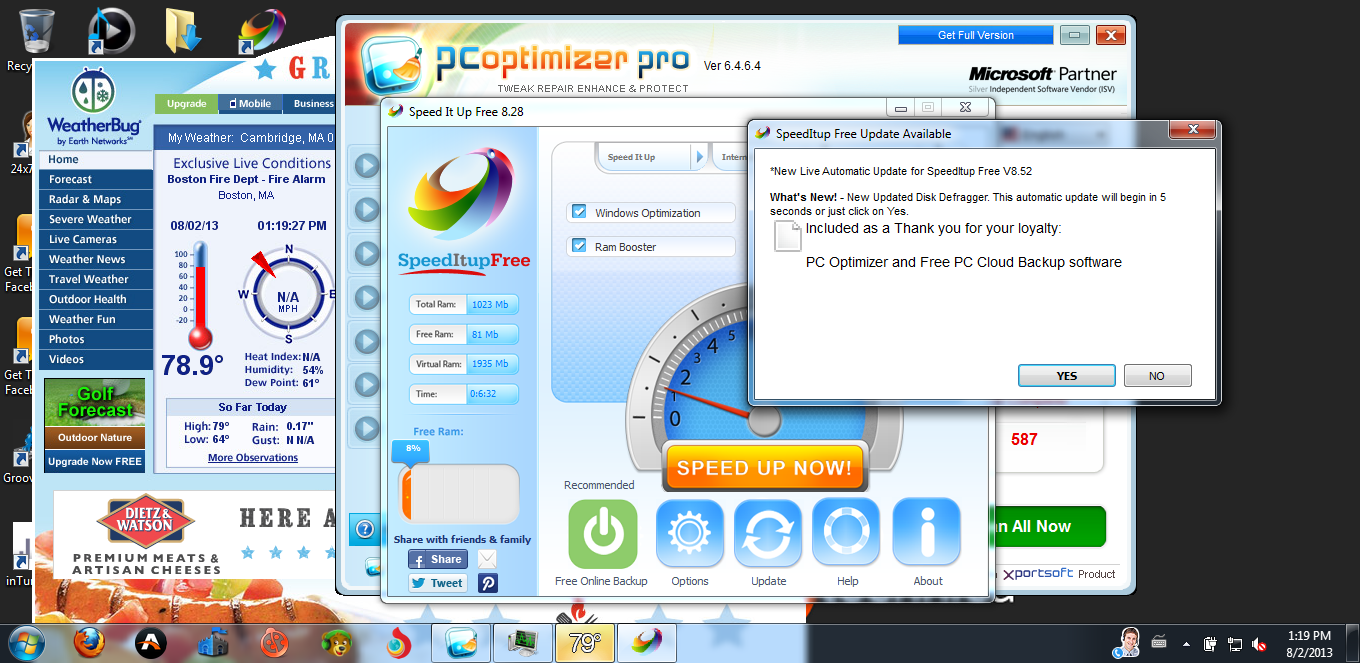 Enlarge / This automatic update will begin in five seconds or just click on Yes. I saw this notification, buried behind other pop-up windows after startup, more than five seconds after it first appeared. More free stuff!
Enlarge / This automatic update will begin in five seconds or just click on Yes. I saw this notification, buried behind other pop-up windows after startup, more than five seconds after it first appeared. More free stuff!
Conor Myhrvold
Restart and repeat. Two of the Windows updates didnt install properly, so I fought off additional adware upgrades and updates to re-install. At least SpeedItUp had the decency to nominally ask for permission. My PC Backup started the installation wizard without any prompts. By this point, I had seen enough. I killed as many adware-running processes as I could and watched as the install processes worked their way to the top. (The updates completed installing just a few minutes afterward.) In total, it took six hours of getting my computer down to speed on performance to get it up to speed on updates.
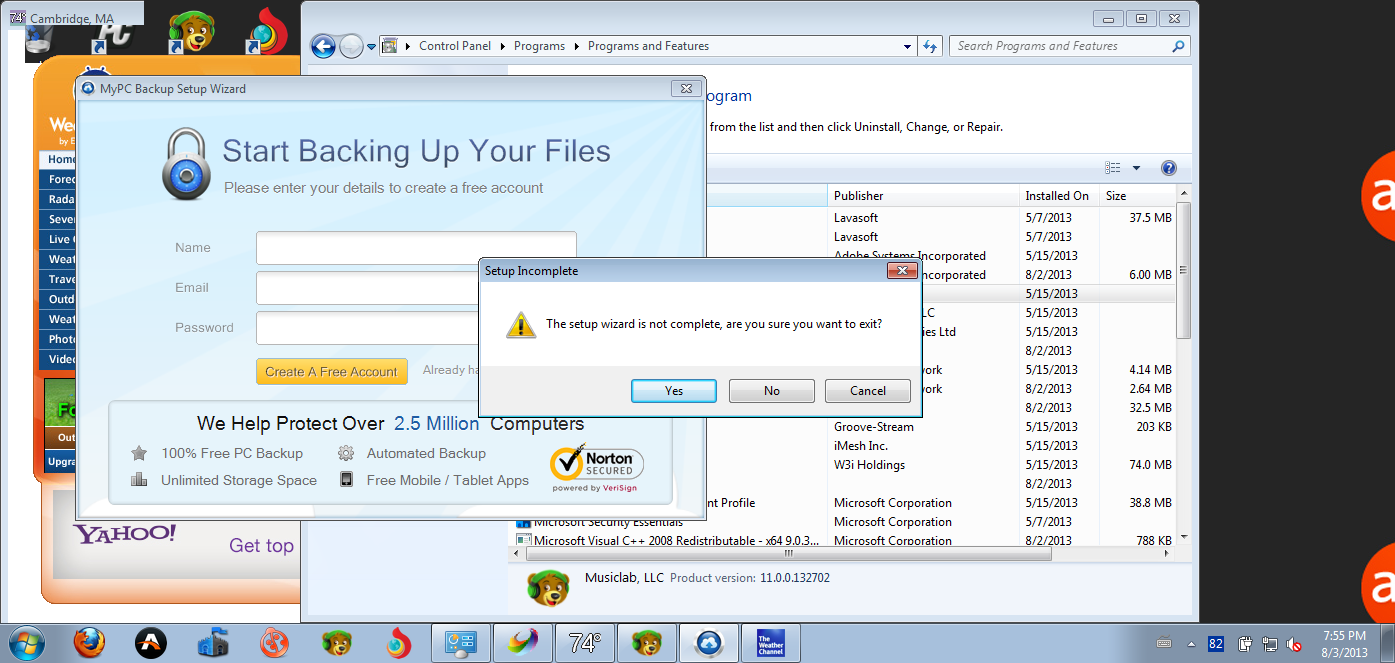 Enlarge / Complications? You don't say...
Enlarge / Complications? You don't say...
Conor Myhrvold
In order to see the uninstallation improvement, I decided to take a free music downloads adware inventory to see what I was dealing with compared to my original plain vanilla Windows 7 install. Taking the tally of my Control Panel yielded the first surprise. As it turns out, several programs installed that Id forgotten about, since they didnt make their presence known on the desktop or in Firefox extensions/plugins: an executable file of the Ask Toolbar, Sea App by Growth Systems LLC (Internet Explorer-only), and Music Oasis by W3i, LLC. That brought the initial program count to 18 programs (19 if you consider the Internet Explorer-only app to be a program).
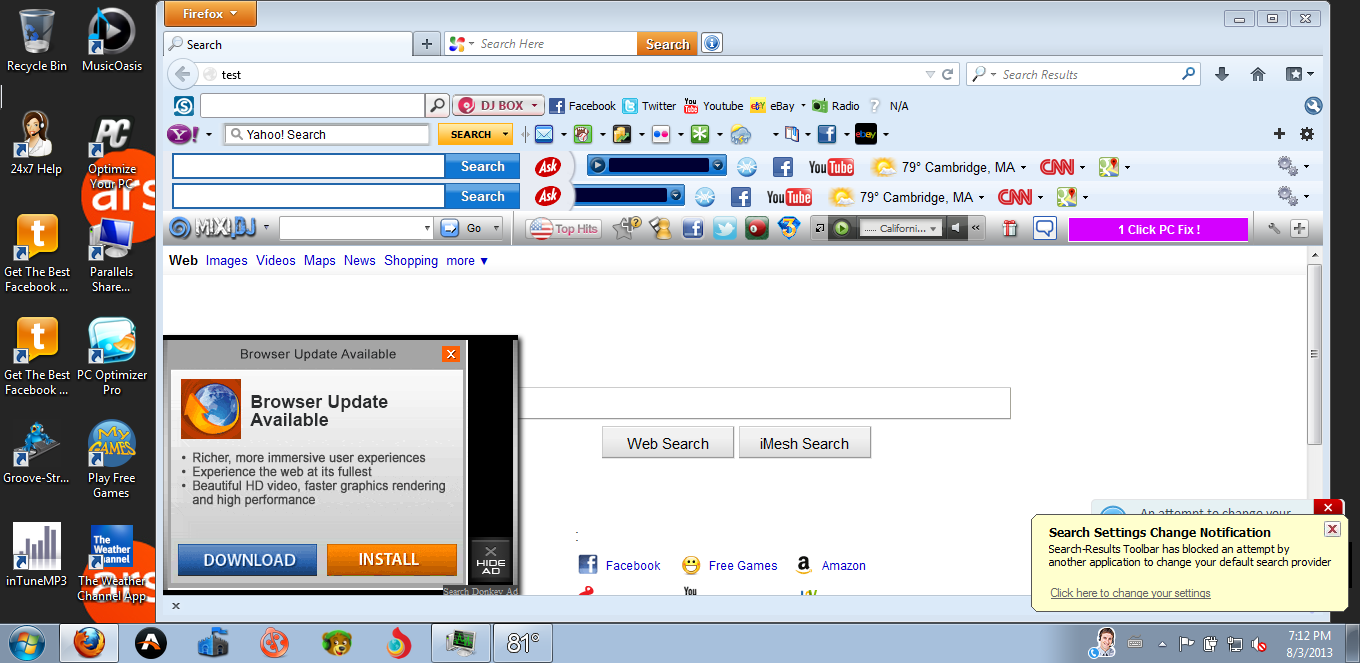 Enlarge / My free music downloads Firefox browser at its worst, before attempted uninstalls.
Enlarge / My free music downloads Firefox browser at its worst, before attempted uninstalls.
Conor Myhrvold
In the image above, note the unstable oscillations between the blue and yellow Search Settings notification wars. These were ongoing, flickering back and forth in the lower right corner of my screen. Apparently I installed duplicate Ask Toolbars. I was able to uninstall one with difficulty, but not the other. Ask once, youll be in trouble. Ask again and apparently youll be Ask-ing forever!
In the adware updating that took place, I upgraded FrostWire, SpeedItUp, and PC Optimizer Pro. That last update also included an automatic installation of My PC Backup. I clicked on the Exit window and closed it, but this didnt actually stop the installation. This is a known tactic both McAfees PUP Report and the DEFCON 18 talk My Life as a Spyware Developer warned about. The additional version of the Ask Toolbar apparently became FrostWires Samaritan and savior in the process (Installing this component will ensure the future of FrostWire! said the splash window text). According to the Control Panel, somewhere in all of this my Free Rides Games Player added two more passengers: Mahjong Mysteries of the Past and My Farm Life 2. All aboard, I supposelet the benchmarking begin.
I used default settings for space allocation in making my virtual machine2GBso additional processes primarily resulted in a delay time until launch. Nevertheless, my CPU and memory usage still shot up to hover constantly close to 100 percent after the downloads when compared to my Plain Vanilla version. The new programs created a big backlog for the adware infested version, and the running processes increased from 44 to 77 by default (that is, without opening any programs or touching anything in either case after a computer restart).
I also noticed a sharp uptick in startup processes. Fourteen new ones appeared in the free music downloads version, along with three applications which were running upon startup. (That's up from zero in the Plain Vanilla OS.) I was getting a lot for no money. It was time to try to rid myself of the freebies which were costing me no money, just so much time.
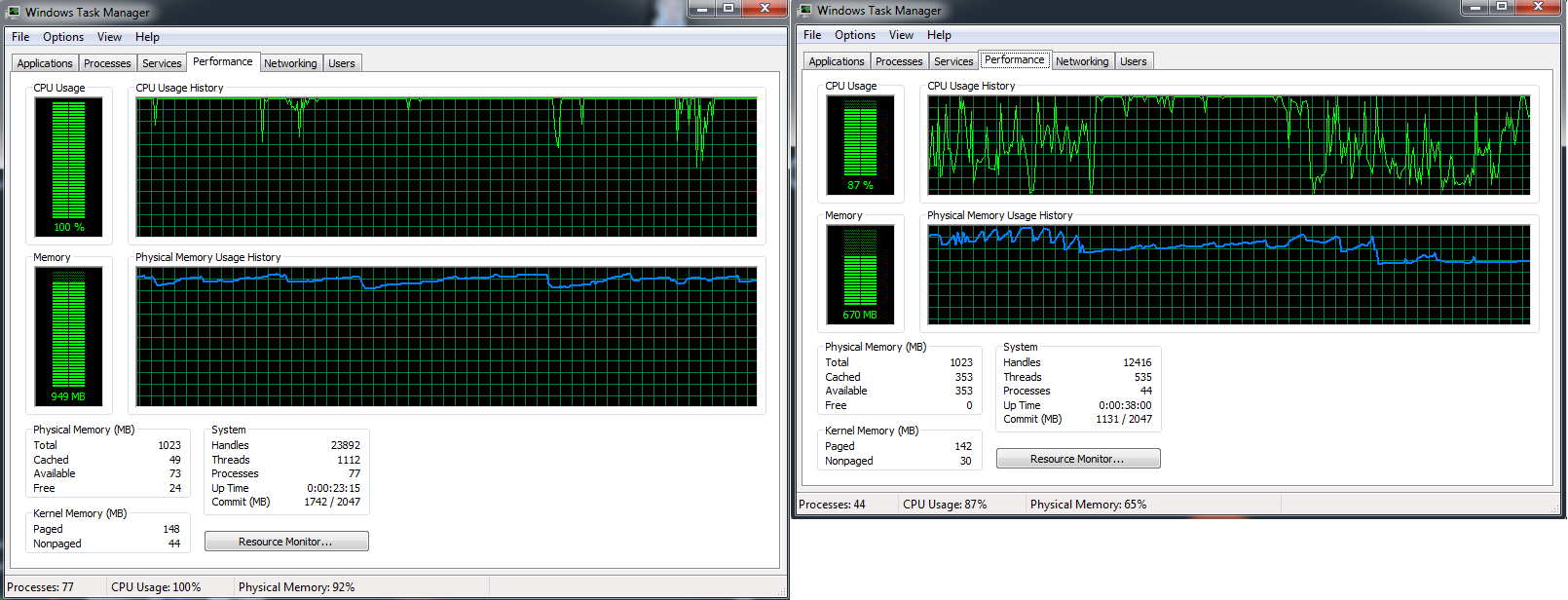 Enlarge / The left Task Manager window is the adware-infested OS, while the right is that same system before all of the installs.
Enlarge / The left Task Manager window is the adware-infested OS, while the right is that same system before all of the installs.
Conor Myhrvold
Desktop version Task Manager apps Running processes Sys Config startup processes Firefox memory usage upon opening Time to open browser and search "test" Plain Vanilla (Windows 7 install) 0 44 5 ~75M Less than 10s Post-"free music" downloads 3 77 19 ~300M More than 12m (19m to access extensions, plugins) Sys Config Startup Processes (Additions from Plain Vanilla to Post-Download): 14
Yontoo Desktop by Yontoo LLC, WeatherBug Desktop by AWS Convergence Technologies, Inc., EXETender Client by Exent Technologies Ltd., Search Protect by Conduit, Smartbar by Smartbar, BearShare by MusicLab, LLC, The Weather Channel App by The Weather Channel, SpeedItUp Free by MicroSmarts LLC., Data Manager by iMesh Inc., Search Protect by Conduit, PC Fix Speed by Crawler.com, 24x7Help by Crawler, LLC, ASK TBNotifier by APN, FrostWire by Frostwire.
Task Manager Apps (Additions from Plain Vanilla to Post-Download): 3
Weatherbug, PC Fix Speed, The Weather Channel App
Part II: The Control Panel surprise
My first uninstall targets were the Firefox Extensions and Plugins. To disable them, I embarked on what would be an ambitious strategy on my adware-laden computerI would need to start Firefox. Firefox.exes journey from the bottom of the Task Manager to the top was fraught with unresponsiveness, threats of Windows Explorer crashes, and a long wait time. It all reminded me of AC/DCs first hit song, "Its A Long Way to the Top (If You Wanna Rock n Roll)." This wasnt as thrilling of an adventure, though. It didnt leave me hanging so much as it left itself hanging, a lot.
 Enlarge / I tried to get going on my Firefox extension and plugin uninstalls. But after clicking on Firefox, it had to slowly climb its way through a plethora of processes, mostly adware, as it gained enough memory allocation to launch the browser window and then respond to a search.
Enlarge / I tried to get going on my Firefox extension and plugin uninstalls. But after clicking on Firefox, it had to slowly climb its way through a plethora of processes, mostly adware, as it gained enough memory allocation to launch the browser window and then respond to a search.
Conor Myhrvold
Eventually, Firefox made it to the top over the many svchost.exe and adware processes. A blank browser appeared for several minutes. The browser window responded and promptly went unresponsive, flickering back and forth, all the while gaining memory and moving up toward the top. Its inevitability at seizing the top spot (slowly) became apparent.
First, a visual of the toolbar outlines, then the occasional flash, reminded me that fixing my PC was one click away. The multitude of toolbar icons were up and running. Almost 20 minutes later, I was finally able to rock and roll and start my crippling campaign against the invasive plugins and extensions. Firefox had not only reached the top of the Task Manager, but it seized the number one spot and was now dominating all the other ones. The browser ballooned up to 400M of memory. (For comparison, in the Plain Vanilla OS, Firefox almost immediately loadsin several secondsand consumes 40 to 60M of memory.) The increase in space usage was likely toolbars and adware reporting back on my computer specs to their makers. I saw address after unrecognizable address appear in the bottom left as the browser was loading, sending information to the adwares mysterious controllers around the world.
But the adware kingdoms hegemony and intrusions into the inner workings of my OS were about to end. Firefoxs extensions and plugins would be extended no more, living up to their temporary and expendable namesakes. To give my computer liberty, I would give them death. For the most part, I was able to disable my plugins and extensions without difficulty. Several displayed duplicitous messages to stay. Mixi DJ threw up a new window and recommended hiding the toolbar instead of uninstalling (thus obviating the whole alleged use of the toolbar in the first place). The We Care App opened another Firefox window with a survey asking why I removed it. Neither are standard fare for removing extensions and plugins. But in half an hour, my Firefox extensions and plugins succumbed to the simple disable feature on Firefox. And though I would discover that some would leave remnants on my main computer, they at least left Firefox for good.
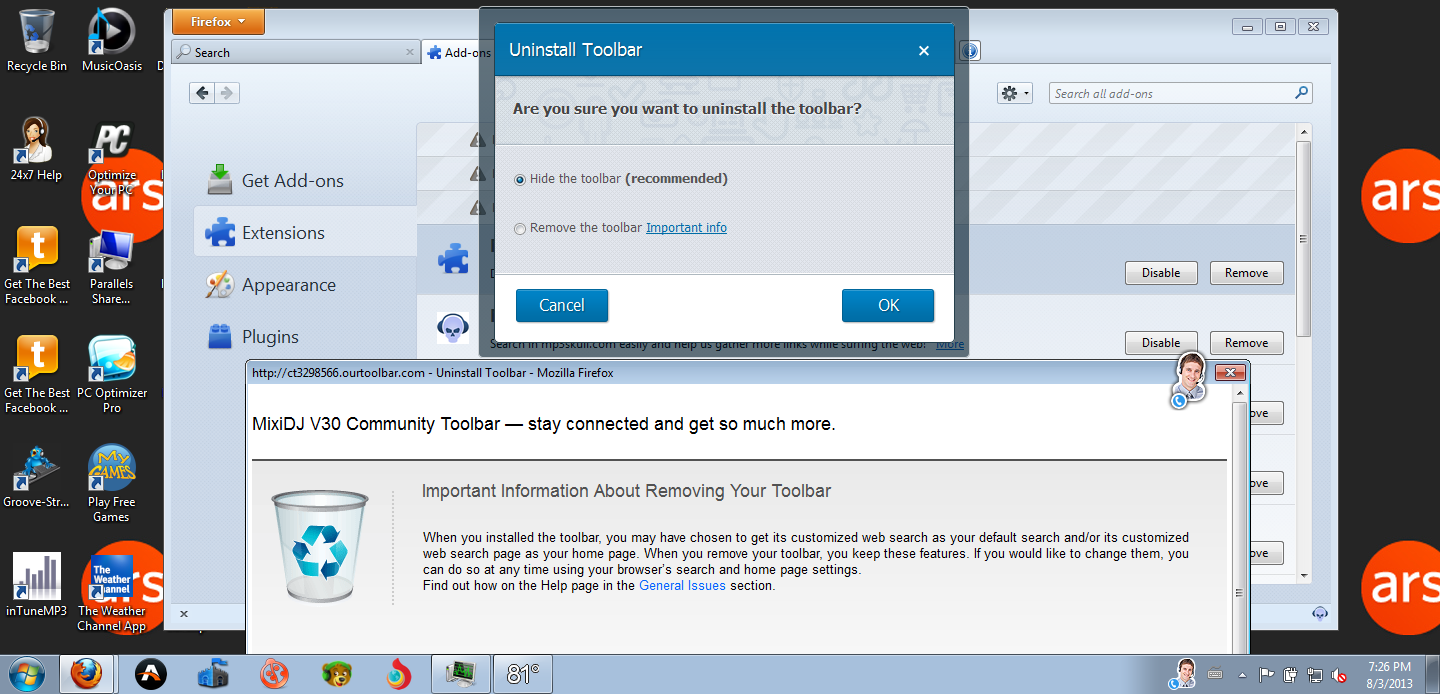 Enlarge / Mixi DJs plea to stay on your computerit will stay out of your way and wont make a peep, it promises!
Enlarge / Mixi DJs plea to stay on your computerit will stay out of your way and wont make a peep, it promises!
Conor Myhrvold
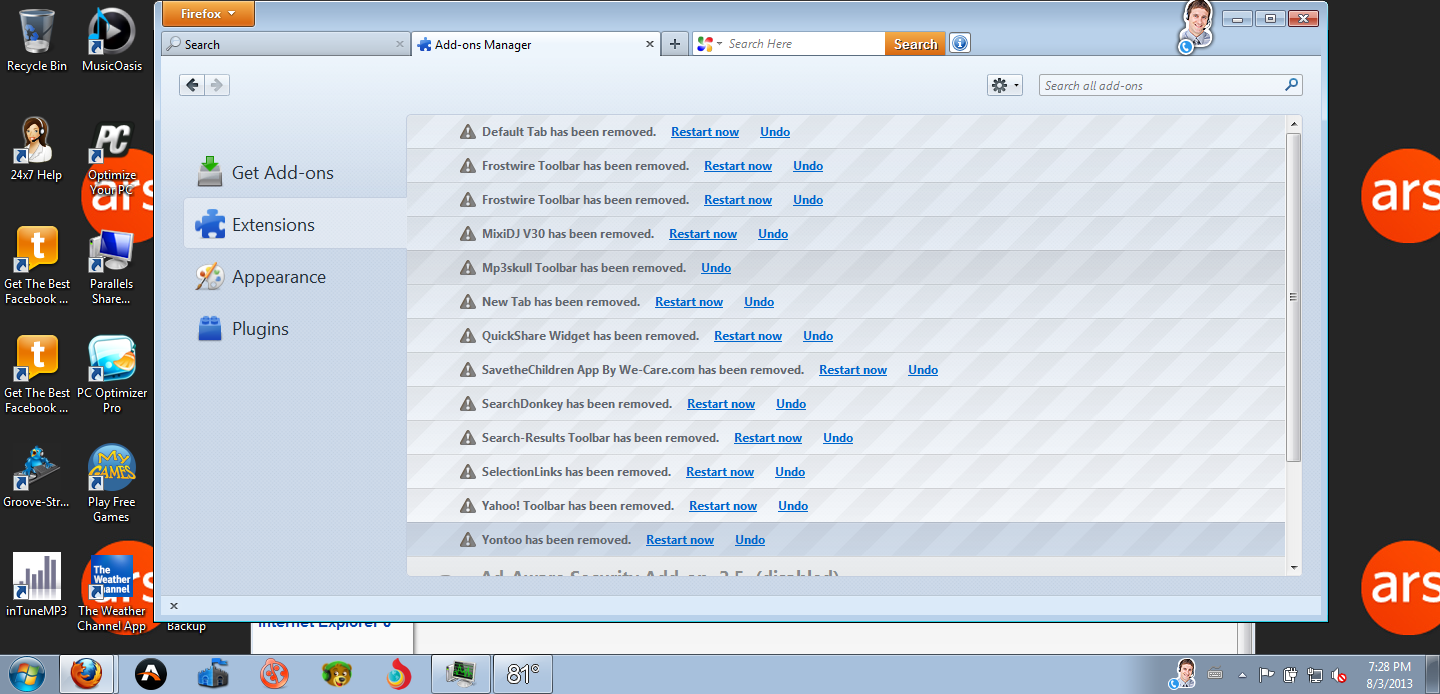 Enlarge / Once I was in to the Add-ons and Extensions manager, disabling everything was a relative breeze. Away with thee, plugins and extensions! Simply exhilarating.
Enlarge / Once I was in to the Add-ons and Extensions manager, disabling everything was a relative breeze. Away with thee, plugins and extensions! Simply exhilarating.
Conor Myhrvold
But that only solved part of the slow problem. With my computer still sluggish, it was time to take more decisive actions. I ended all adware tasks on the Task Manager to see how many programs I could uninstall on my own. Firefox restarted faster, this time taking only about seven minutes. I was actually a bit overzealous, and in ending a vital Windows process (that sounded suspicious to me) I inadvertently blue-screened my computer. Despite that minor hiccup, I was up and running a few minutes later.
I uninstalled programs in alphabetical order using the straightforward Control Panel Add/Remove Program tool, like I would use for any program. For the most part, amazingly, this worked. This was easily the biggest surprise from this experiment.
Some programs fought harder than others to stay on the computer. The first setting of 7 Wonders II (the first program on my list) checked preserve settings and info by default, which meant it didnt fully install. It had a mentality of dont hate the player, hate the game. But I did hate the Free Rides Games Player. No more free ride for it, and leaving the player on my computer was not what I had intended. Bad PUP! I tried again, unchecking the option. Game over.
When I got to F, my computer froze in the middle of uninstalling FrostWire. No activity, the screen was just frozen (the clock too). After unsuccessful troubleshooting for 20 minutes, I forced a restart. Strangely, it later appeared that FrostWire uninstalled. Sort of. Only one of the two FrostWire Ask Toolbars would uninstall. The original version from May, not the newer version, troubled me.
Unsurprisingly, iMesh couldnt uninstall, and it threw up an error. It was one of many programs that had the Uninstall helper unchecked by default in my previous experiment. However, I was eventually able to uninstall iMesh from the Control Panel. I went to its webpage and found (in a more obscure portion of the site ) that if I downloaded iMesh again, reinstalling the update over the original, then it could be uninstalled using the Control Panel. It took me about 10 minutes of searching to find this out, and few users are likely to discover it since its a counterintuitive hack: installing the adware again that youre trying to get rid of in the first place.
The MixiDJ V30 Community Toolbar was next. In the middle of uninstalling, it opened up an Internet Explorer browser (scary enough, I know, but it gets worse). An IE click prompt appeared: Speed up browsing by disabling add-ons. Surely it must be a perfunctory message; I never opened Internet Explorer. But I clicked anyway, and to my dismay there they all were, a long list of PUPs delaying my IE browser. The Quick Share Widget was by far the worst, delaying launch by 9.29 seconds. Combined, the adware lived up to its name, adding between 12 and 15 seconds in browser load time. Why didnt I simply sum up the amounts, you ask? Well, shortly after taking a screenshot of the total, my computer froze once again. After briefly unfreezing, even the Parallels Restart button didnt work. Yikes. After several minutes of troubleshooting, I eventually managed to shut the Virtual Machine down, albeit improperly, and upon restart Mixi DJ was gone.
PC Optimizer Pro asked whether I want to Clean All Now in a green button or Uninstall now. Nice try, but it really didnt want me to go. The program brought me to its webpage and a live chat appeared: Thanks for stopping by! Can I help you with anything? Curiosity got the better of me and I responded, No thanks; just trying to uninstall." No answer. I closed the browser and a Firefox message appeared. This page is asking you to confirm that you want to leave. Yes, I did want to leave. I hit enter, and the same message reappeared. Yes, I still wanted to leave. I hit enter again and the browser finally closed.
Save the Children Reminder, a former Firefox foe I thought Id already vanquished, threw up a shameless message that I was saving children by merely having the app on my computer. Of course, it could help a variety of other causes, too. But I wasnt convinced, and after uninstalling I was presented with the same questionnaire as happened in Firefox.
SpeedItUp Free threw up a message where the default option was to not uninstall. But when I clicked yes, it uninstalled quickly. Next was The Sea App (Internet Explorer-only) I never knew I had. I made it the No-See App in short order. Then the Weather Channel App. A Wise Installation Wizard thought for a few seconds and the app then tried to keep me with the same option choice where the default was to leave it on my computer. I was now down to my final adware program on first pass, the dreaded Yontoo. It warned me to close my browsers to uninstall properly. But boom, a second later it was gone in an anti-climactic finish.
Finally, I went back and uninstalled Adobe AIR and the Flash Player 11 Plugin, which arent adware, but I still downloaded them from my "free music" downloads search. Ironically, Adobe AIR wont let me uninstall since it says uninstallation might not be allowed by the administrator (I am the administrator). Now just Adobe AIR and a (FrostWire branded) Ask Toolbar were left, as was a Get the Best Facebook Chat Messenger shortcut which I promptly trashed. Superficially, my desktop finally looked like it did in the Plain Vanilla original. But there was still some work to do. Just to make sure, I opened Internet Explorer again to see if everything was gone from there.
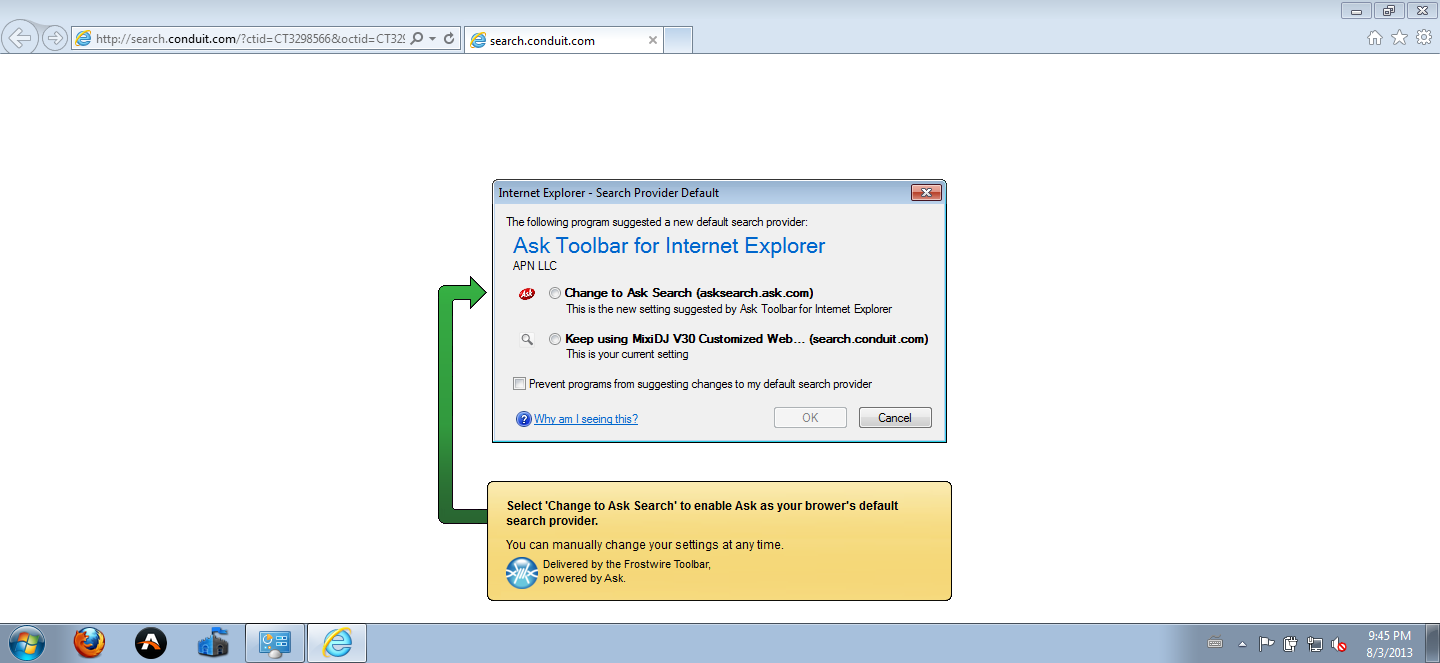
I was soon prevented with a Faustian bargain: should I change to Ask or keep using MixiDJV30? What?! I looked more closely in Internet Explorer and there, it turns out, was the Ask toolbar, the MixiDJ toolbar, and several others as well. I tried to disable everything and restart IE. Now the Ask toolbar has been, in fact, supplanted by MixiDJ. I hit the toolbar window in the upper right and an ad flashed in the main browser window. Uh oh. I was now definitely done playing games removing the remaining, peskiest PUPs.
Three hours in, it was time to bring out some heavy artillerya list of five free recommended anti-PUP programs to put to the test. I had spent my entire evening uninstalling programs by this point. Letting the programs run away, I would fight them another day.
 Enlarge / Both choices are bad, so I opted for neither. By hitting cancel, I created a victor in Mixi DJ.
Enlarge / Both choices are bad, so I opted for neither. By hitting cancel, I created a victor in Mixi DJ.
Conor Myhrvold
Part II: The Control Panel surprise
My first uninstall targets were the Firefox Extensions and Plugins. To disable them, I embarked on what would be an ambitious strategy on my adware-laden computerI would need to start Firefox. Firefox.exes journey from the bottom of the Task Manager to the top was fraught with unresponsiveness, threats of Windows Explorer crashes, and a long wait time. It all reminded me of AC/DCs first hit song, "Its A Long Way to the Top (If You Wanna Rock n Roll)." This wasnt as thrilling of an adventure, though. It didnt leave me hanging so much as it left itself hanging, a lot.
 Enlarge / I tried to get going on my Firefox extension and plugin uninstalls. But after clicking on Firefox, it had to slowly climb its way through a plethora of processes, mostly adware, as it gained enough memory allocation to launch the browser window and then respond to a search.
Enlarge / I tried to get going on my Firefox extension and plugin uninstalls. But after clicking on Firefox, it had to slowly climb its way through a plethora of processes, mostly adware, as it gained enough memory allocation to launch the browser window and then respond to a search.
Conor Myhrvold
Eventually, Firefox made it to the top over the many svchost.exe and adware processes. A blank browser appeared for several minutes. The browser window responded and promptly went unresponsive, flickering back and forth, all the while gaining memory and moving up toward the top. Its inevitability at seizing the top spot (slowly) became apparent.
First, a visual of the toolbar outlines, then the occasional flash, reminded me that fixing my PC was one click away. The multitude of toolbar icons were up and running. Almost 20 minutes later, I was finally able to rock and roll and start my crippling campaign against the invasive plugins and extensions. Firefox had not only reached the top of the Task Manager, but it seized the number one spot and was now dominating all the other ones. The browser ballooned up to 400M of memory. (For comparison, in the Plain Vanilla OS, Firefox almost immediately loadsin several secondsand consumes 40 to 60M of memory.) The increase in space usage was likely toolbars and adware reporting back on my computer specs to their makers. I saw address after unrecognizable address appear in the bottom left as the browser was loading, sending information to the adwares mysterious controllers around the world.
But the adware kingdoms hegemony and intrusions into the inner workings of my OS were about to end. Firefoxs extensions and plugins would be extended no more, living up to their temporary and expendable namesakes. To give my computer liberty, I would give them death. For the most part, I was able to disable my plugins and extensions without difficulty. Several displayed duplicitous messages to stay. Mixi DJ threw up a new window and recommended hiding the toolbar instead of uninstalling (thus obviating the whole alleged use of the toolbar in the first place). The We Care App opened another Firefox window with a survey asking why I removed it. Neither are standard fare for removing extensions and plugins. But in half an hour, my Firefox extensions and plugins succumbed to the simple disable feature on Firefox. And though I would discover that some would leave remnants on my main computer, they at least left Firefox for good.
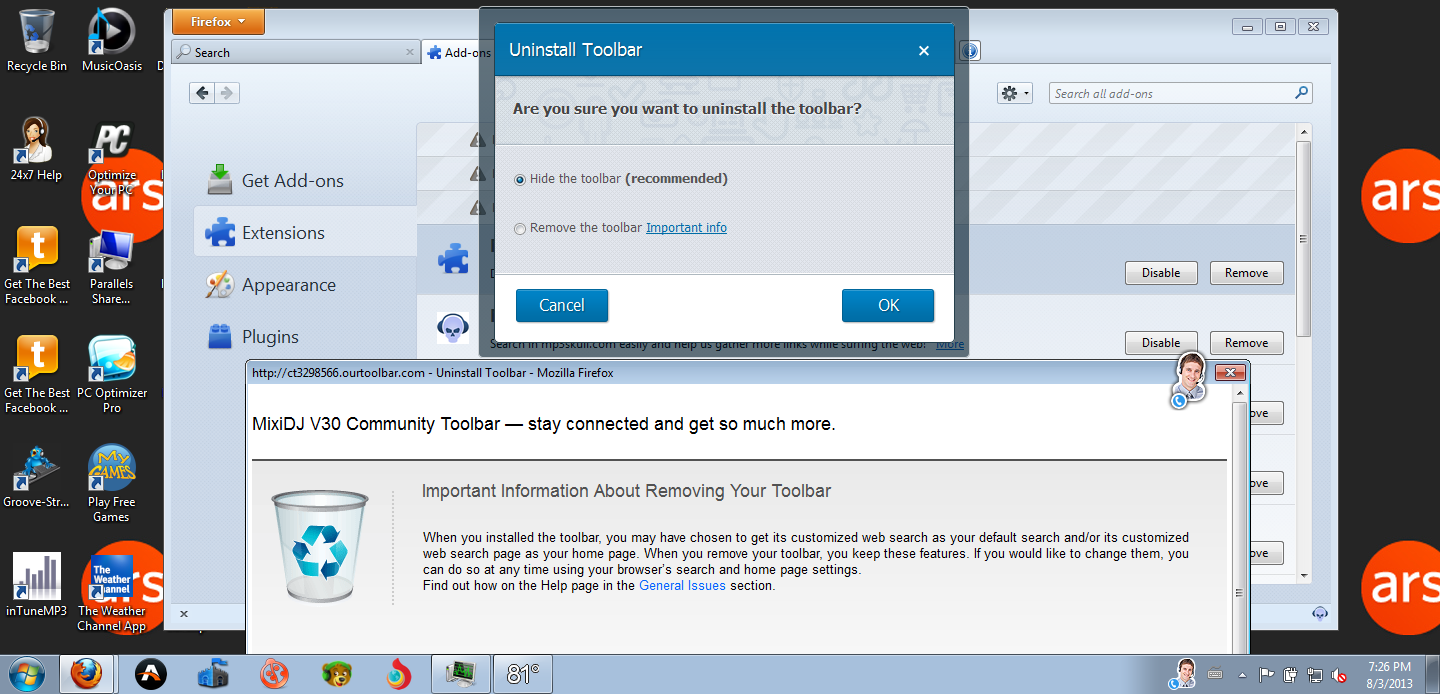 Enlarge / Mixi DJs plea to stay on your computerit will stay out of your way and wont make a peep, it promises!
Enlarge / Mixi DJs plea to stay on your computerit will stay out of your way and wont make a peep, it promises!
Conor Myhrvold
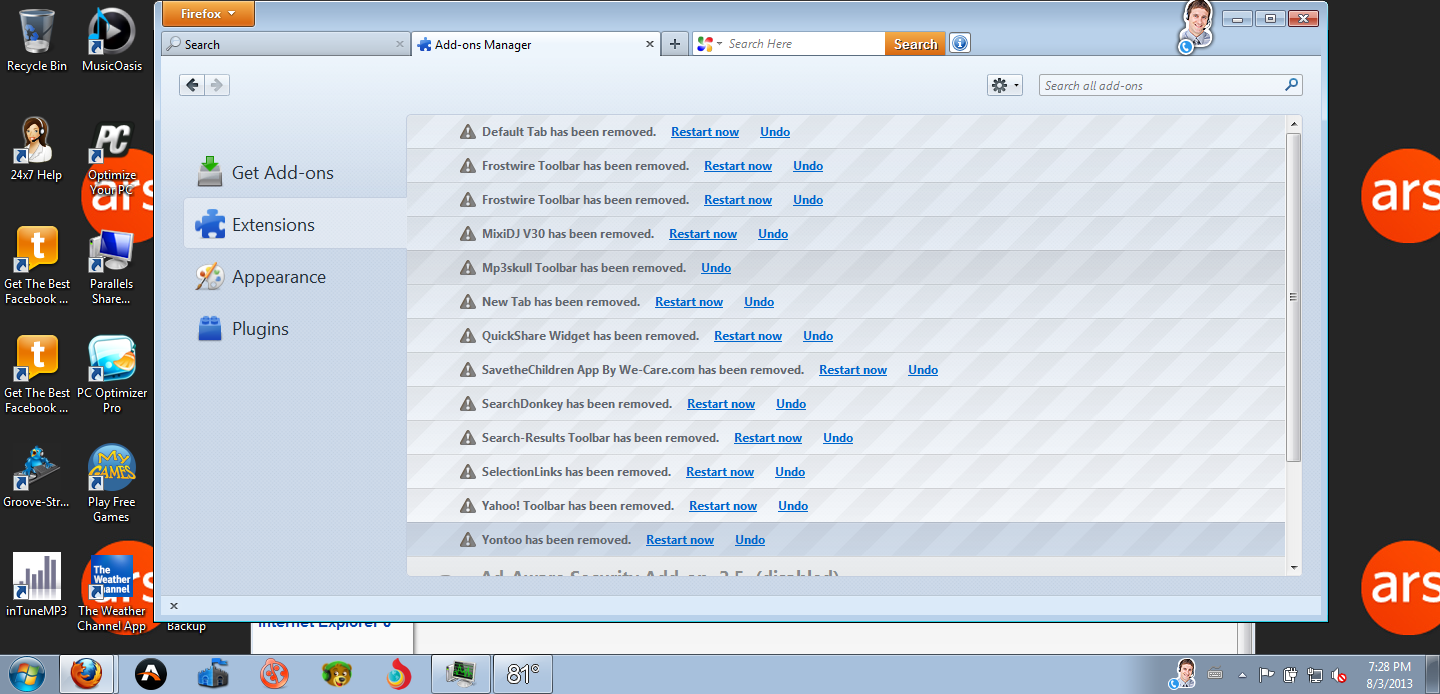 Enlarge / Once I was in to the Add-ons and Extensions manager, disabling everything was a relative breeze. Away with thee, plugins and extensions! Simply exhilarating.
Enlarge / Once I was in to the Add-ons and Extensions manager, disabling everything was a relative breeze. Away with thee, plugins and extensions! Simply exhilarating.
Conor Myhrvold
But that only solved part of the slow problem. With my computer still sluggish, it was time to take more decisive actions. I ended all adware tasks on the Task Manager to see how many programs I could uninstall on my own. Firefox restarted faster, this time taking only about seven minutes. I was actually a bit overzealous, and in ending a vital Windows process (that sounded suspicious to me) I inadvertently blue-screened my computer. Despite that minor hiccup, I was up and running a few minutes later.
I uninstalled programs in alphabetical order using the straightforward Control Panel Add/Remove Program tool, like I would use for any program. For the most part, amazingly, this worked. This was easily the biggest surprise from this experiment.
Some programs fought harder than others to stay on the computer. The first setting of 7 Wonders II (the first program on my list) checked preserve settings and info by default, which meant it didnt fully install. It had a mentality of dont hate the player, hate the game. But I did hate the Free Rides Games Player. No more free ride for it, and leaving the player on my computer was not what I had intended. Bad PUP! I tried again, unchecking the option. Game over.
When I got to F, my computer froze in the middle of uninstalling FrostWire. No activity, the screen was just frozen (the clock too). After unsuccessful troubleshooting for 20 minutes, I forced a restart. Strangely, it later appeared that FrostWire uninstalled. Sort of. Only one of the two FrostWire Ask Toolbars would uninstall. The original version from May, not the newer version, troubled me.
Unsurprisingly, iMesh couldnt uninstall, and it threw up an error. It was one of many programs that had the Uninstall helper unchecked by default in my previous experiment. However, I was eventually able to uninstall iMesh from the Control Panel. I went to its webpage and found (in a more obscure portion of the site ) that if I downloaded iMesh again, reinstalling the update over the original, then it could be uninstalled using the Control Panel. It took me about 10 minutes of searching to find this out, and few users are likely to discover it since its a counterintuitive hack: installing the adware again that youre trying to get rid of in the first place.
The MixiDJ V30 Community Toolbar was next. In the middle of uninstalling, it opened up an Internet Explorer browser (scary enough, I know, but it gets worse). An IE click prompt appeared: Speed up browsing by disabling add-ons. Surely it must be a perfunctory message; I never opened Internet Explorer. But I clicked anyway, and to my dismay there they all were, a long list of PUPs delaying my IE browser. The Quick Share Widget was by far the worst, delaying launch by 9.29 seconds. Combined, the adware lived up to its name, adding between 12 and 15 seconds in browser load time. Why didnt I simply sum up the amounts, you ask? Well, shortly after taking a screenshot of the total, my computer froze once again. After briefly unfreezing, even the Parallels Restart button didnt work. Yikes. After several minutes of troubleshooting, I eventually managed to shut the Virtual Machine down, albeit improperly, and upon restart Mixi DJ was gone.
PC Optimizer Pro asked whether I want to Clean All Now in a green button or Uninstall now. Nice try, but it really didnt want me to go. The program brought me to its webpage and a live chat appeared: Thanks for stopping by! Can I help you with anything? Curiosity got the better of me and I responded, No thanks; just trying to uninstall." No answer. I closed the browser and a Firefox message appeared. This page is asking you to confirm that you want to leave. Yes, I did want to leave. I hit enter, and the same message reappeared. Yes, I still wanted to leave. I hit enter again and the browser finally closed.
Save the Children Reminder, a former Firefox foe I thought Id already vanquished, threw up a shameless message that I was saving children by merely having the app on my computer. Of course, it could help a variety of other causes, too. But I wasnt convinced, and after uninstalling I was presented with the same questionnaire as happened in Firefox.
SpeedItUp Free threw up a message where the default option was to not uninstall. But when I clicked yes, it uninstalled quickly. Next was The Sea App (Internet Explorer-only) I never knew I had. I made it the No-See App in short order. Then the Weather Channel App. A Wise Installation Wizard thought for a few seconds and the app then tried to keep me with the same option choice where the default was to leave it on my computer. I was now down to my final adware program on first pass, the dreaded Yontoo. It warned me to close my browsers to uninstall properly. But boom, a second later it was gone in an anti-climactic finish.
Finally, I went back and uninstalled Adobe AIR and the Flash Player 11 Plugin, which arent adware, but I still downloaded them from my "free music" downloads search. Ironically, Adobe AIR wont let me uninstall since it says uninstallation might not be allowed by the administrator (I am the administrator). Now just Adobe AIR and a (FrostWire branded) Ask Toolbar were left, as was a Get the Best Facebook Chat Messenger shortcut which I promptly trashed. Superficially, my desktop finally looked like it did in the Plain Vanilla original. But there was still some work to do. Just to make sure, I opened Internet Explorer again to see if everything was gone from there.
I was soon prevented with a Faustian bargain: should I change to Ask or keep using MixiDJV30? What?! I looked more closely in Internet Explorer and there, it turns out, was the Ask toolbar, the MixiDJ toolbar, and several others as well. I tried to disable everything and restart IE. Now the Ask toolbar has been, in fact, supplanted by MixiDJ. I hit the toolbar window in the upper right and an ad flashed in the main browser window. Uh oh. I was now definitely done playing games removing the remaining, peskiest PUPs.
Three hours in, it was time to bring out some heavy artillerya list of five free recommended anti-PUP programs to put to the test. I had spent my entire evening uninstalling programs by this point. Letting the programs run away, I would fight them another day.
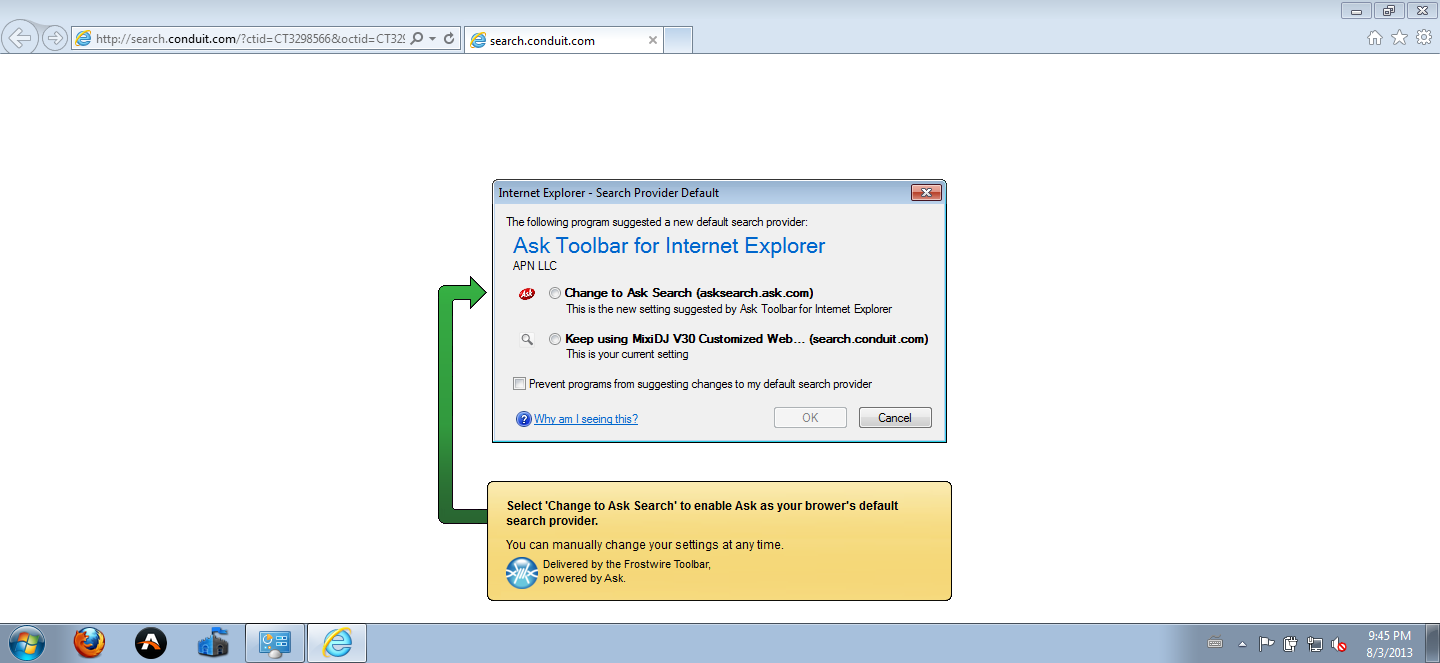 Enlarge / Both choices are bad, so I opted for neither. By hitting cancel, I created a victor in Mixi DJ.
Enlarge / Both choices are bad, so I opted for neither. By hitting cancel, I created a victor in Mixi DJ.
Conor Myhrvold
Part II: The Control Panel surprise
My first uninstall targets were the Firefox Extensions and Plugins. To disable them, I embarked on what would be an ambitious strategy on my adware-laden computerI would need to start Firefox. Firefox.exes journey from the bottom of the Task Manager to the top was fraught with unresponsiveness, threats of Windows Explorer crashes, and a long wait time. It all reminded me of AC/DCs first hit song, "Its A Long Way to the Top (If You Wanna Rock n Roll)." This wasnt as thrilling of an adventure, though. It didnt leave me hanging so much as it left itself hanging, a lot.
 Enlarge / I tried to get going on my Firefox extension and plugin uninstalls. But after clicking on Firefox, it had to slowly climb its way through a plethora of processes, mostly adware, as it gained enough memory allocation to launch the browser window and then respond to a search.
Enlarge / I tried to get going on my Firefox extension and plugin uninstalls. But after clicking on Firefox, it had to slowly climb its way through a plethora of processes, mostly adware, as it gained enough memory allocation to launch the browser window and then respond to a search.
Conor Myhrvold
Eventually, Firefox made it to the top over the many svchost.exe and adware processes. A blank browser appeared for several minutes. The browser window responded and promptly went unresponsive, flickering back and forth, all the while gaining memory and moving up toward the top. Its inevitability at seizing the top spot (slowly) became apparent.
First, a visual of the toolbar outlines, then the occasional flash, reminded me that fixing my PC was one click away. The multitude of toolbar icons were up and running. Almost 20 minutes later, I was finally able to rock and roll and start my crippling campaign against the invasive plugins and extensions. Firefox had not only reached the top of the Task Manager, but it seized the number one spot and was now dominating all the other ones. The browser ballooned up to 400M of memory. (For comparison, in the Plain Vanilla OS, Firefox almost immediately loadsin several secondsand consumes 40 to 60M of memory.) The increase in space usage was likely toolbars and adware reporting back on my computer specs to their makers. I saw address after unrecognizable address appear in the bottom left as the browser was loading, sending information to the adwares mysterious controllers around the world.
But the adware kingdoms hegemony and intrusions into the inner workings of my OS were about to end. Firefoxs extensions and plugins would be extended no more, living up to their temporary and expendable namesakes. To give my computer liberty, I would give them death. For the most part, I was able to disable my plugins and extensions without difficulty. Several displayed duplicitous messages to stay. Mixi DJ threw up a new window and recommended hiding the toolbar instead of uninstalling (thus obviating the whole alleged use of the toolbar in the first place). The We Care App opened another Firefox window with a survey asking why I removed it. Neither are standard fare for removing extensions and plugins. But in half an hour, my Firefox extensions and plugins succumbed to the simple disable feature on Firefox. And though I would discover that some would leave remnants on my main computer, they at least left Firefox for good.
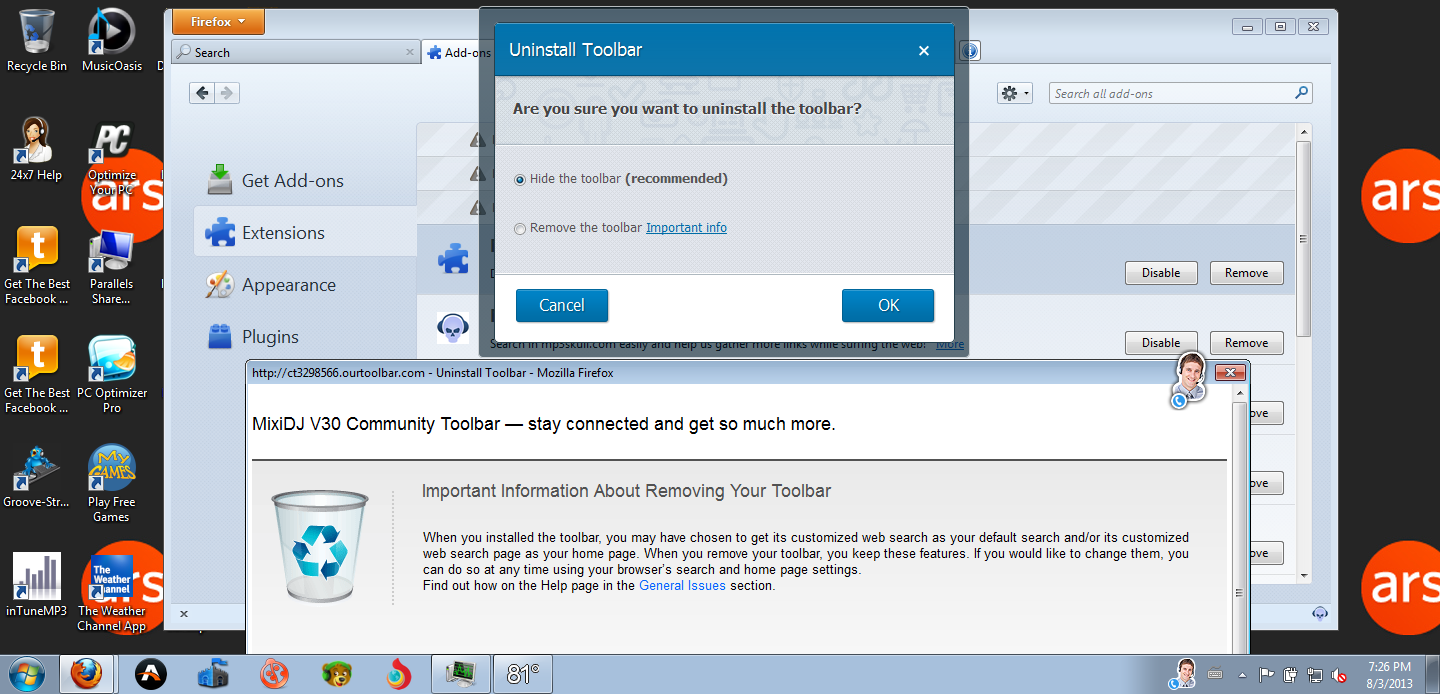 Enlarge / Mixi DJs plea to stay on your computerit will stay out of your way and wont make a peep, it promises!
Enlarge / Mixi DJs plea to stay on your computerit will stay out of your way and wont make a peep, it promises!
Conor Myhrvold
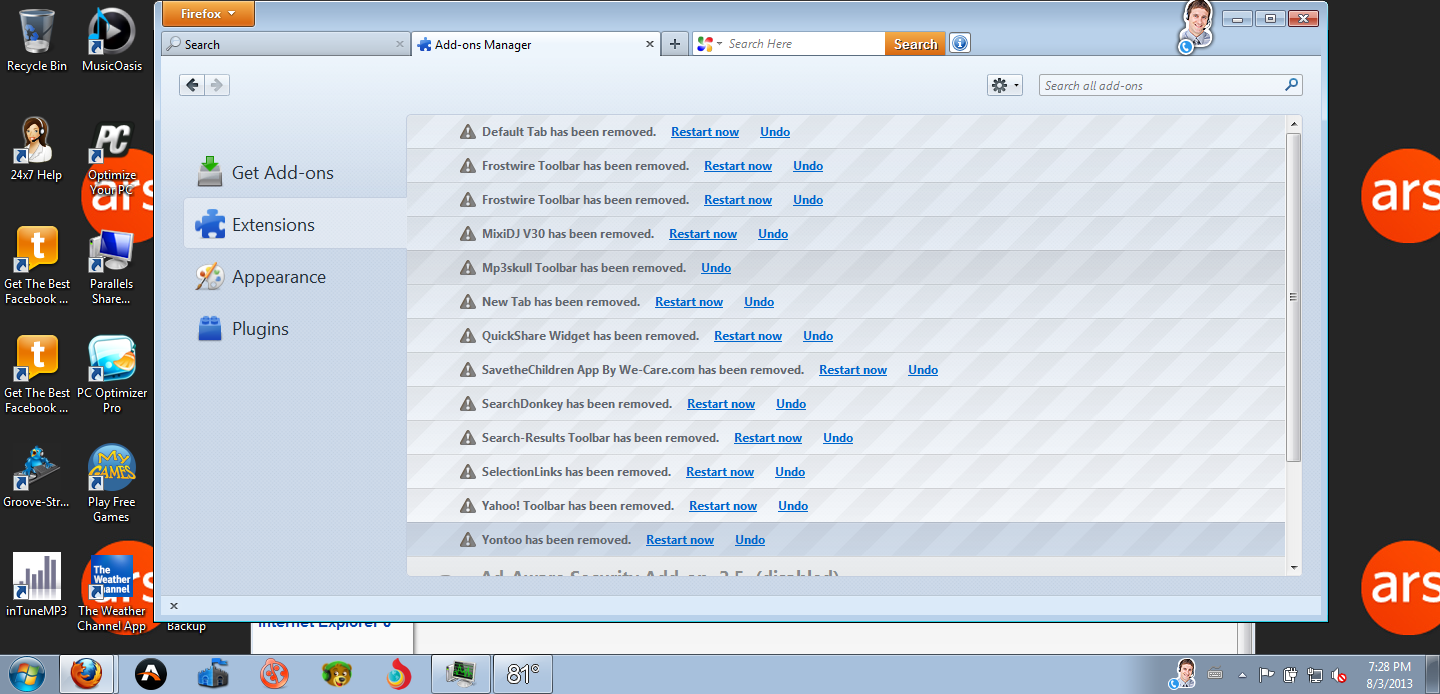 Enlarge / Once I was in to the Add-ons and Extensions manager, disabling everything was a relative breeze. Away with thee, plugins and extensions! Simply exhilarating.
Enlarge / Once I was in to the Add-ons and Extensions manager, disabling everything was a relative breeze. Away with thee, plugins and extensions! Simply exhilarating.
Conor Myhrvold
But that only solved part of the slow problem. With my computer still sluggish, it was time to take more decisive actions. I ended all adware tasks on the Task Manager to see how many programs I could uninstall on my own. Firefox restarted faster, this time taking only about seven minutes. I was actually a bit overzealous, and in ending a vital Windows process (that sounded suspicious to me) I inadvertently blue-screened my computer. Despite that minor hiccup, I was up and running a few minutes later.
I uninstalled programs in alphabetical order using the straightforward Control Panel Add/Remove Program tool, like I would use for any program. For the most part, amazingly, this worked. This was easily the biggest surprise from this experiment.
Some programs fought harder than others to stay on the computer. The first setting of 7 Wonders II (the first program on my list) checked preserve settings and info by default, which meant it didnt fully install. It had a mentality of dont hate the player, hate the game. But I did hate the Free Rides Games Player. No more free ride for it, and leaving the player on my computer was not what I had intended. Bad PUP! I tried again, unchecking the option. Game over.
When I got to F, my computer froze in the middle of uninstalling FrostWire. No activity, the screen was just frozen (the clock too). After unsuccessful troubleshooting for 20 minutes, I forced a restart. Strangely, it later appeared that FrostWire uninstalled. Sort of. Only one of the two FrostWire Ask Toolbars would uninstall. The original version from May, not the newer version, troubled me.
Unsurprisingly, iMesh couldnt uninstall, and it threw up an error. It was one of many programs that had the Uninstall helper unchecked by default in my previous experiment. However, I was eventually able to uninstall iMesh from the Control Panel. I went to its webpage and found (in a more obscure portion of the site ) that if I downloaded iMesh again, reinstalling the update over the original, then it could be uninstalled using the Control Panel. It took me about 10 minutes of searching to find this out, and few users are likely to discover it since its a counterintuitive hack: installing the adware again that youre trying to get rid of in the first place.
The MixiDJ V30 Community Toolbar was next. In the middle of uninstalling, it opened up an Internet Explorer browser (scary enough, I know, but it gets worse). An IE click prompt appeared: Speed up browsing by disabling add-ons. Surely it must be a perfunctory message; I never opened Internet Explorer. But I clicked anyway, and to my dismay there they all were, a long list of PUPs delaying my IE browser. The Quick Share Widget was by far the worst, delaying launch by 9.29 seconds. Combined, the adware lived up to its name, adding between 12 and 15 seconds in browser load time. Why didnt I simply sum up the amounts, you ask? Well, shortly after taking a screenshot of the total, my computer froze once again. After briefly unfreezing, even the Parallels Restart button didnt work. Yikes. After several minutes of troubleshooting, I eventually managed to shut the Virtual Machine down, albeit improperly, and upon restart Mixi DJ was gone.
PC Optimizer Pro asked whether I want to Clean All Now in a green button or Uninstall now. Nice try, but it really didnt want me to go. The program brought me to its webpage and a live chat appeared: Thanks for stopping by! Can I help you with anything? Curiosity got the better of me and I responded, No thanks; just trying to uninstall." No answer. I closed the browser and a Firefox message appeared. This page is asking you to confirm that you want to leave. Yes, I did want to leave. I hit enter, and the same message reappeared. Yes, I still wanted to leave. I hit enter again and the browser finally closed.
Save the Children Reminder, a former Firefox foe I thought Id already vanquished, threw up a shameless message that I was saving children by merely having the app on my computer. Of course, it could help a variety of other causes, too. But I wasnt convinced, and after uninstalling I was presented with the same questionnaire as happened in Firefox.
SpeedItUp Free threw up a message where the default option was to not uninstall. But when I clicked yes, it uninstalled quickly. Next was The Sea App (Internet Explorer-only) I never knew I had. I made it the No-See App in short order. Then the Weather Channel App. A Wise Installation Wizard thought for a few seconds and the app then tried to keep me with the same option choice where the default was to leave it on my computer. I was now down to my final adware program on first pass, the dreaded Yontoo. It warned me to close my browsers to uninstall properly. But boom, a second later it was gone in an anti-climactic finish.
Finally, I went back and uninstalled Adobe AIR and the Flash Player 11 Plugin, which arent adware, but I still downloaded them from my "free music" downloads search. Ironically, Adobe AIR wont let me uninstall since it says uninstallation might not be allowed by the administrator (I am the administrator). Now just Adobe AIR and a (FrostWire branded) Ask Toolbar were left, as was a Get the Best Facebook Chat Messenger shortcut which I promptly trashed. Superficially, my desktop finally looked like it did in the Plain Vanilla original. But there was still some work to do. Just to make sure, I opened Internet Explorer again to see if everything was gone from there.
I was soon prevented with a Faustian bargain: should I change to Ask or keep using MixiDJV30? What?! I looked more closely in Internet Explorer and there, it turns out, was the Ask toolbar, the MixiDJ toolbar, and several others as well. I tried to disable everything and restart IE. Now the Ask toolbar has been, in fact, supplanted by MixiDJ. I hit the toolbar window in the upper right and an ad flashed in the main browser window. Uh oh. I was now definitely done playing games removing the remaining, peskiest PUPs.
Three hours in, it was time to bring out some heavy artillerya list of five free recommended anti-PUP programs to put to the test. I had spent my entire evening uninstalling programs by this point. Letting the programs run away, I would fight them another day.
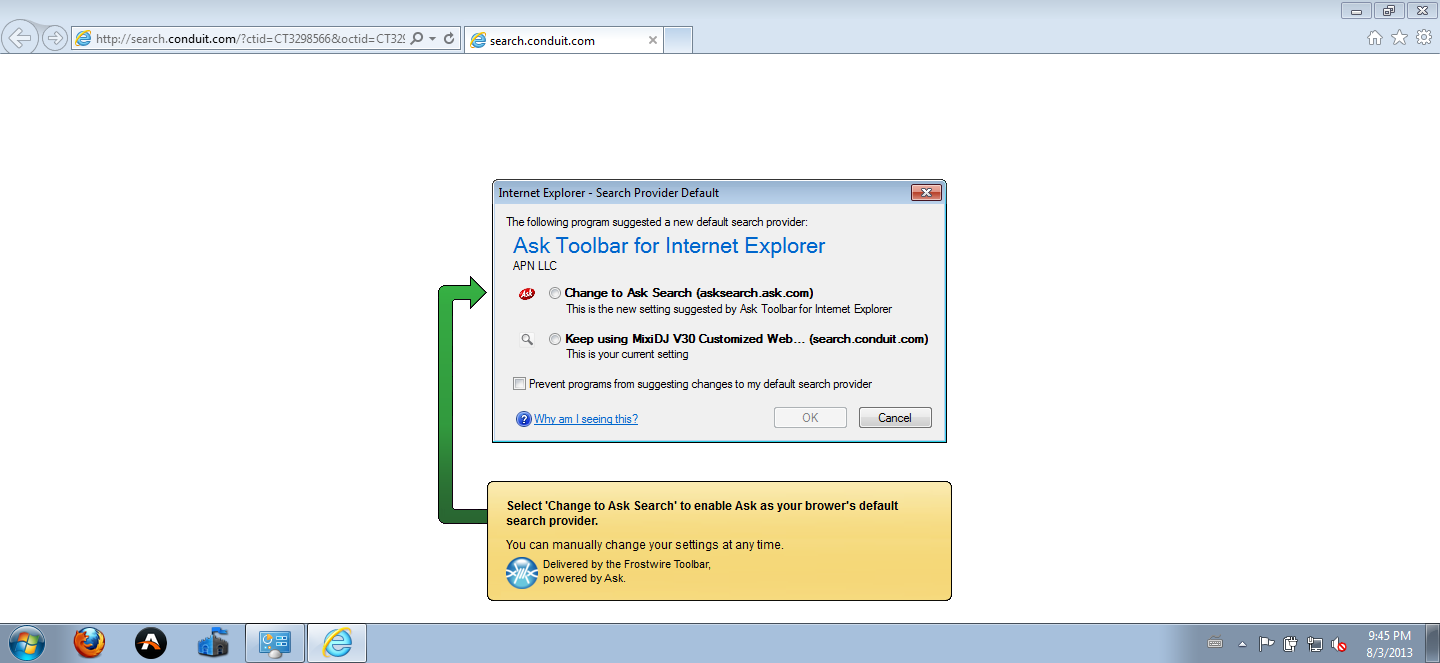 Enlarge / Both choices are bad, so I opted for neither. By hitting cancel, I created a victor in Mixi DJ.
Enlarge / Both choices are bad, so I opted for neither. By hitting cancel, I created a victor in Mixi DJ.
Conor Myhrvold
Part III: Experimenting with the final PUPs
I found a list of the top five free malware removal programs on Lifehacker: Spybot Search & Destroy, SUPERAntiSpyware, Combofix, Malware Bytes Anti Malwares, and Trend Micros HijackThis. The last option came with the ability to post the log file on hijackthis.de, which automatically analyzed the file and then, from crowdsourced feedback, suggested which programs to uninstall. Malware Bytes was in particular well-regarded in the comments, so I was excited to see what these collated crusaders against PUPs could do for my machine.
This brief section reflects my disappointment in the results. None of the tools were able to remove or even detect the last of my programs. They failed as badly as my Microsoft Security Essentials and AdAware results, in either the Quick Scan or Full Scan modes. However, HijackThis did detect and remove other adware remnants of already uninstalled programs, orphaned folder skeletons strewn across my computer where programs used to live like an adware ghost town. And iMesh was still on my computer this whole time. I only went to its website in desperation after these five programs failed to find it, let alone remove it. These two were the last of the PUPs:Adobe AIRBecause I'm not one to admit defeat, I wound up installing two other programs to try to remove the Ask Toolbar and Adobe AIR. These proposed solutions came from searching forums on how to get rid of iMesh and Ask: Revo Uninstaller and Mighty Uninstaller. Revo was able to uninstall Adobe AIR in its forced removal setting, along with a folder containing an 18MB Ask.exe file that I never would have known about. However, the FrostWire-induced Ask Toolbar logo stayed on my computer. Let's call that a partial victory after a little over two hours using specialized toolsIve neutralized Ask on my computer. This PUP has been neutered and put in the pound. Its not in IE or Firefox and there are no executable files left that I could find using Windows Explorer.
What it does: Manages Adobe installations.
Not a bad program, but it wanted administrator privileges to uninstall. I was, of course, the administrator the whole time. Clicking run as administrator didnt help, either.
Ask Toolbar (branded by Frostwire, an Ask Partner)
What it does: Zombie reincarnation of a once legitimate search option.
Clutters your browser, acts as the go-to point for searching and homepage, and redirects that information to potential third parties and whoever its trusted and valued partners are (in other words, who can reliably pay it). Oracle shamefully bundles this toolbar with Java by default, hoping that you wont stop to unclick installing it with each new Java update thats pushed out.
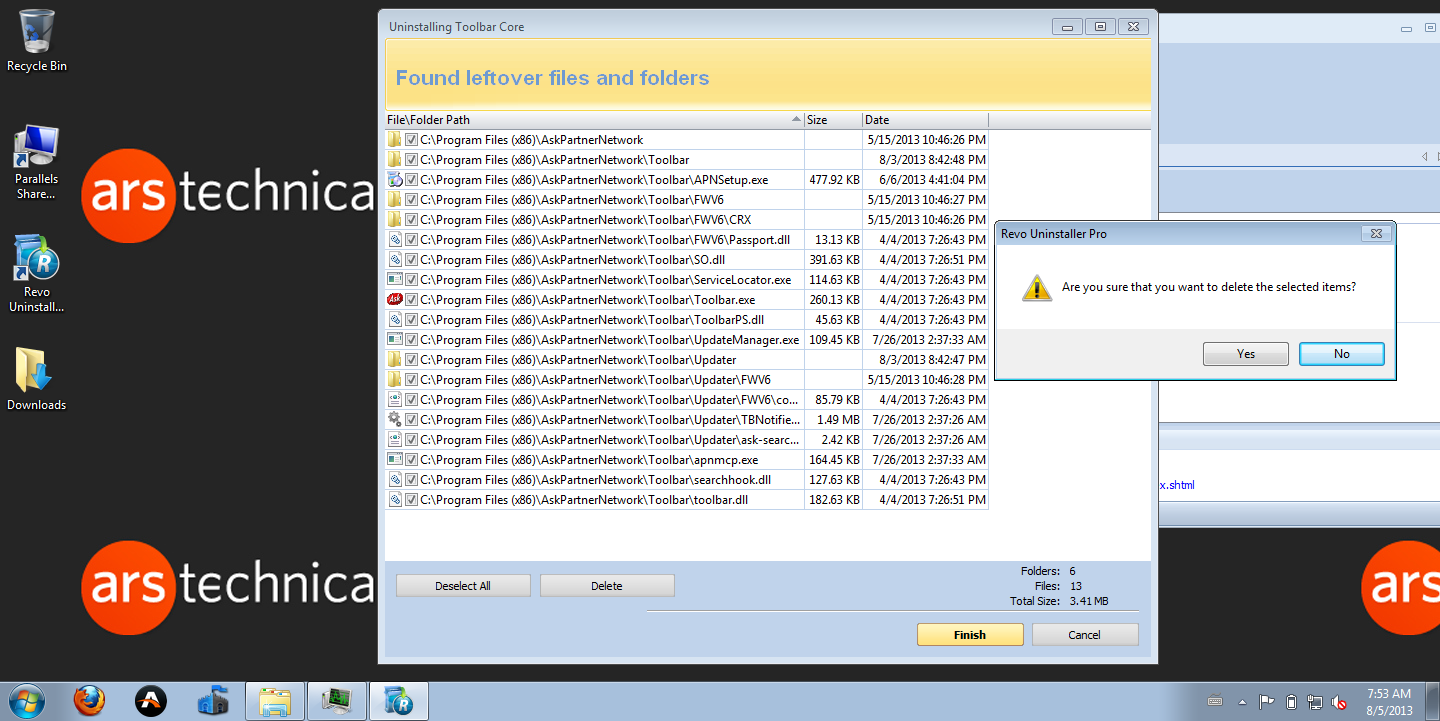 Enlarge / The trial version of the Revo Uninstaller removed Adobe AIR in addition to part of the Ask Toolbar, which the Control Panel and the other anti-PUP programs did not detect.
Enlarge / The trial version of the Revo Uninstaller removed Adobe AIR in addition to part of the Ask Toolbar, which the Control Panel and the other anti-PUP programs did not detect.
Conor Myhrvold
Part IV: Get your PUPs spayed and neutered
I learned that you can rid yourself of most adware programs using the normal uninstaller, even iMesh and Yontoo and their hard-to-kill reputations. But the Ask Toolbar, which Oracle shamefully bundles with its Java updates to bring its clinginess to the masses, left remnants I was unable to remove.
In the end, you dont play with the PUPs; PUPs play with you. They are time-consuming, badly behaved, and unlike their furry likeness, they are more likely to earn you pity than adulation from strangers on the street. (They will, perhaps, entertain younger children if there is a game component, which often seems to be the target audience for some of the adware I downloaded.)
According to a McAfees diagnosis, most of the software I installed exhibited typical PUP behavior. They covered spyware (sending information about the computer to third parties), adware (pop-ups and deceptive pay-to-play software), and browser hijackers (redirecting the homepage and search service to a new default automatically and without warning). A few even stretched into more serious Trojan behavior, appearing to commandeer the Layered Service Provider.
The five malware programs I tried found tracking cookies but little else. This does not mean that these malware removal software tools are useless, but rather theyre largely not needed for adware I encountered during my search for freebies. In most cases, I was able to uninstall the adware programs the same way you would uninstall any other type of software on your computerwith the caveat that the adware would try to Wormtongue its way into talking you out of it. From the performance specs, however, if untreated, the adware downloaded rendered my computer completely unusable.
If you were just handed a computer, a search for adware using HijackThis gives a quick overview of what you have on your computer. But if you watched the windows carefully through the programs protests and pleas, a straightforward uninstall can rid you of adware like the kind I encountered when searching for free stuff.
My Plain Vanilla install removal took three hours, and the specialized tools took a little over two hours. After five hours of work, my computer showed no traces of running adware applications or performance issues. It ran like new, albeit with Ask toolbar traces and other bits and pieces of programs which were like battle scars from the war on PUPs. The continued presence of some form of FrostWires Ask toolbar has made me question whether well ever be able to evolve programs capable of removing the most pernicious PUPs. Its indicative of an overall trend in the adware/malware war, a bleak outlook on whether the programs that act like ticks and burrs to our computers will ever be able to be out-Firefoxed without hours of attentive work to remove them.
The cost of installing the adware was free, but the cost of removal for an IT professional is high. You have to pay attention to what youre doing to successfully remove many of the programsselecting default settings will keep many programs on the computer (by design). The adware is winning so long as programs like FrostWire continue to bundle up with Ask. Winter is coming.
 Enlarge / Serenity now.
Enlarge / Serenity now.
Conor Myhrvold
Whats the moral of the story? That Windows is more trouble that its worth, live and learn. ReciprocityIn questions of power let no more be heard of confidence in man, but bind him down from mischief by the chains of the Constitution. Thomas Jefferson
-
08-30-2013, 02:25 AM #44Senior Member


- Join Date
- Jan 2006
- Location
- tracking the usurper-in-chief and on his trail
- Posts
- 3,208
One man's terrorist is another man's undocumented worker.
Unless we enforce laws against illegal aliens today,
tomorrow WE may wake up as illegals.
The last word: illegal aliens are ILLEGAL!
-
08-30-2013, 08:47 AM #45Banned

- Join Date
- Jun 2013
- Posts
- 8,506
Download me IIRemoving the remnants of the Webs most dangerous search terms
Who knew that "free" could lead to a PUP? (Sadly, not the cute and cuddly kind.)
by Conor Myhrvold Aug 25, 2013 10:00 pm UTC
It gives me a headache!!!!!
-
09-05-2013, 09:07 PM #46
How to remain secure against NSA surveillance
The NSA has huge capabilities and if it wants in to your computer, it's in. With that in mind, here are five ways to stay safe
-

- Bruce Schneier
- theguardian.com, Thursday 5 September 2013 15.06 EDT
- Jump to comments (249)
 'Trust the math. Encryption is your friend. That's how you can remain secure even in the face of the NSA.' Photograph: Beck Diefenbach/Reuters
'Trust the math. Encryption is your friend. That's how you can remain secure even in the face of the NSA.' Photograph: Beck Diefenbach/Reuters
Now that we have enough details about how the NSA eavesdrops on the internet, including today's disclosures of the NSA's deliberate weakening of cryptographic systems, we can finally start to figure out how to protect ourselves.
For the past two weeks, I have been working with the Guardian on NSA stories, and have read hundreds of top-secret NSA documents provided by whistleblower Edward Snowden. I wasn't part of today's story it was in process well before I showed up but everything I read confirms what the Guardian is reporting.
At this point, I feel I can provide some advice for keeping secure against such an adversary.
The primary way the NSA eavesdrops on internet communications is in the network. That's where their capabilities best scale. They have invested in enormous programs to automatically collect and analyze network traffic. Anything that requires them to attack individual endpoint computers is significantly more costly and risky for them, and they will do those things carefully and sparingly.
Leveraging its secret agreements with telecommunications companies all the US and UK ones, and many other "partners" around the world the NSA gets access to the communications trunks that move internet traffic. In cases where it doesn't have that sort of friendly access, it does its best to surreptitiously monitor communications channels: tapping undersea cables, intercepting satellite communications, and so on.
That's an enormous amount of data, and the NSA has equivalently enormous capabilities to quickly sift through it all, looking for interesting traffic. "Interesting" can be defined in many ways: by the source, the destination, the content, the individuals involved, and so on. This data is funneled into the vast NSA system for future analysis.
The NSA collects much more metadata about internet traffic: who is talking to whom, when, how much, and by what mode of communication. Metadata is a lot easier to store and analyze than content. It can be extremely personal to the individual, and is enormously valuable intelligence.
The Systems Intelligence Directorate is in charge of data collection, and the resources it devotes to this is staggering. I read status report after status report about these programs, discussing capabilities, operational details, planned upgrades, and so on. Each individual problem recovering electronic signals from fiber, keeping up with the terabyte streams as they go by, filtering out the interesting stuff has its own group dedicated to solving it. Its reach is global.
The NSA also attacks network devices directly: routers, switches, firewalls, etc. Most of these devices have surveillance capabilities already built in; the trick is to surreptitiously turn them on. This is an especially fruitful avenue of attack; routers are updated less frequently, tend not to have security software installed on them, and are generally ignored as a vulnerability.
The NSA also devotes considerable resources to attacking endpoint computers. This kind of thing is done by its TAO Tailored Access Operations group. TAO has a menu of exploits it can serve up against your computer whether you're running Windows, Mac OS, Linux, iOS, or something else and a variety of tricks to get them on to your computer. Your anti-virus software won't detect them, and you'd have trouble finding them even if you knew where to look. These are hacker tools designed by hackers with an essentially unlimited budget. What I took away from reading the Snowden documents was that if the NSA wants in to your computer, it's in. Period.
The NSA deals with any encrypted data it encounters more by subverting the underlying cryptography than by leveraging any secret mathematical breakthroughs. First, there's a lot of bad cryptography out there. If it finds an internet connection protected by MS-CHAP, for example, that's easy to break and recover the key. It exploits poorly chosen user passwords, using the same dictionary attacks hackers use in the unclassified world.
As was revealed today, the NSA also works with security product vendors to ensure that commercial encryption products are broken in secret ways that only it knows about. We know this has happened historically: CryptoAG and Lotus Notes are the most public examples, and there is evidence of a back door in Windows. A few people have told me some recent stories about their experiences, and I plan to write about them soon. Basically, the NSA asks companies to subtly change their products in undetectable ways: making the random number generator less random, leaking the key somehow, adding a common exponent to a public-key exchange protocol, and so on. If the back door is discovered, it's explained away as a mistake. And as we now know, the NSA has enjoyed enormous success from this program.
TAO also hacks into computers to recover long-term keys. So if you're running a VPN that uses a complex shared secret to protect your data and the NSA decides it cares, it might try to steal that secret. This kind of thing is only done against high-value targets.
How do you communicate securely against such an adversary? Snowden said it in an online Q&A soon after he made his first document public: "Encryption works. Properly implemented strong crypto systems are one of the few things that you can rely on."
I believe this is true, despite today's revelations and tantalizing hints of "groundbreaking cryptanalytic capabilities" made by James Clapper, the director of national intelligence in another top-secret document. Those capabilities involve deliberately weakening the cryptography.
Snowden's follow-on sentence is equally important: "Unfortunately, endpoint security is so terrifically weak that NSA can frequently find ways around it."
Endpoint means the software you're using, the computer you're using it on, and the local network you're using it in. If the NSA can modify the encryption algorithm or drop a Trojan on your computer, all the cryptography in the world doesn't matter at all. If you want to remain secure against the NSA, you need to do your best to ensure that the encryption can operate unimpeded.
With all this in mind, I have five pieces of advice:
1) Hide in the network. Implement hidden services. Use Tor to anonymize yourself. Yes, the NSA targets Tor users, but it's work for them. The less obvious you are, the safer you are.
2) Encrypt your communications. Use TLS. Use IPsec. Again, while it's true that the NSA targets encrypted connections and it may have explicit exploits against these protocols you're much better protected than if you communicate in the clear.
3) Assume that while your computer can be compromised, it would take work and risk on the part of the NSA so it probably isn't. If you have something really important, use an air gap. Since I started working with the Snowden documents, I bought a new computer that has never been connected to the internet. If I want to transfer a file, I encrypt the file on the secure computer and walk it over to my internet computer, using a USB stick. To decrypt something, I reverse the process. This might not be bulletproof, but it's pretty good.
4) Be suspicious of commercial encryption software, especially from large vendors. My guess is that most encryption products from large US companies have NSA-friendly back doors, and many foreign ones probably do as well. It's prudent to assume that foreign products also have foreign-installed backdoors. Closed-source software is easier for the NSA to backdoor than open-source software. Systems relying on master secrets are vulnerable to the NSA, through either legal or more clandestine means.
5) Try to use public-domain encryption that has to be compatible with other implementations. For example, it's harder for the NSA to backdoor TLS than BitLocker, because any vendor's TLS has to be compatible with every other vendor's TLS, while BitLocker only has to be compatible with itself, giving the NSA a lot more freedom to make changes. And because BitLocker is proprietary, it's far less likely those changes will be discovered. Prefer symmetric cryptography over public-key cryptography. Prefer conventional discrete-log-based systems over elliptic-curve systems; the latter have constants that the NSA influences when they can.
Since I started working with Snowden's documents, I have been using GPG, Silent Circle, Tails, OTR, TrueCrypt, BleachBit, and a few other things I'm not going to write about. There's an undocumented encryption feature in my Password Safe program from the command line); I've been using that as well.
I understand that most of this is impossible for the typical internet user. Even I don't use all these tools for most everything I am working on. And I'm still primarily on Windows, unfortunately. Linux would be safer.
The NSA has turned the fabric of the internet into a vast surveillance platform, but they are not magical. They're limited by the same economic realities as the rest of us, and our best defense is to make surveillance of us as expensive as possible.
Trust the math. Encryption is your friend. Use it well, and do your best to ensure that nothing can compromise it. That's how you can remain secure even in the face of the NSA.In questions of power let no more be heard of confidence in man, but bind him down from mischief by the chains of the Constitution. Thomas Jefferson
-
-
09-05-2013, 10:43 PM #47
NSA uses supercomputers to crack Web encryption, files show
Snowden documents reveal spy agency campaign to compromise online privacy for national security. nsa. This June 6, 2013, photo shows the sign outside the National Security Agency campus at Fort Meade, Md. . .USA TODAY - 26 minutes ago NO AMNESTY
Don't reward the criminal actions of millions of illegal aliens by giving them citizenship.
Sign in and post comments here.
Please support our fight against illegal immigration by joining ALIPAC's email alerts here https://eepurl.com/cktGTn
-
09-06-2013, 01:06 AM #48
US and UK 'crack online encryption'
BBC News - 4 minutes agoNO AMNESTY
Don't reward the criminal actions of millions of illegal aliens by giving them citizenship.
Sign in and post comments here.
Please support our fight against illegal immigration by joining ALIPAC's email alerts here https://eepurl.com/cktGTn
-
09-09-2013, 04:19 PM #49NO AMNESTY
Don't reward the criminal actions of millions of illegal aliens by giving them citizenship.
Sign in and post comments here.
Please support our fight against illegal immigration by joining ALIPAC's email alerts here https://eepurl.com/cktGTn


 1Likes
1Likes LinkBack URL
LinkBack URL About LinkBacks
About LinkBacks




 Reply With Quote
Reply With Quote


Gov. Hochul Reacts To Homans Vow To Send Surge Of ICE Agents To...
06-09-2026, 12:50 PM in illegal immigration News Stories & Reports